

How Sennovate is helping Mitigate Log4Shell Vulnerabilities
Did you hear about this recently discovered security flaw known as Log4Shell? It’s being called “one of the most serious vulnerability seen in decades,” according to the US Cybersecurity and Infrastructure Security Agency.
The Apache Log4j is a Java library which runs across multiple platforms. It is used by many big companies. Because of its widespread use, the security flaw associated with it affects thousands of web services, including millions of websites and applications.
Let’s dive into detail and learn more about the flaw and its mitigation.
Mitigating Log4Shell vulnerabilities in open source IAM solutions with Sennovate
We at Sennovate work with various IAM solutions and its vendors regularly.
Here is a detailed explanation of how we researched and helped resolve the Log4Shell vulnerability in Gluu
As we all know Gluu is an open source IAM solution that is mainly based on the Java infrastructure. And for all the IAM software generation, logs is an important feature.
From the below article on log management in Gluu we came to know about Gluu is using Log4j library for the logging purpose.
https://gluu.org/docs/gluu-server/4.1/operation/logs/
Our next step of action was to find the version of log4j library used inside the Gluu. Simply running the command locate log4j |grep .jar gave us all the log4j jar file version inside the container. All the versions from 2.0-beta9 to 2.14.1 are vulnerable to Log4Shell.
From here, we now need to find one point of attack where attacker can insert the malicious code.
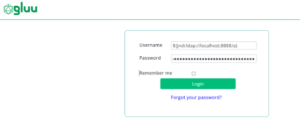
The login page of the Gluu server is one such example, if we open a netcat session on our localhost with port 8888 open using the below command:
nc -nvlp 8888
And then in the login page if we try to make a connection to this session with the code provided as the username.
${jndi:ldap://localhost:8888/a}
We can check our netcat session to receive a connection:
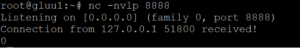
This result is quite disastrous for any server, instead of making a connection to a localhost machine, an attacker can redirect the Gluu server to a server of which he had full control and contains malicious code like malware, crypto miner etc.
How to patch Log4Shell on Gluu server?
The easiest method to mitigate the Log4Shell exploit is to upgrade the log4j library version from 2.14.1 to 2.16.0 and above. Doing this to a running Gluu instance is quite difficult and a lengthy task. Resulting in a large downtime for all the Gluu services.
So one way of mitigation is that we use other mitigation method that we can implement on a running java instance similar like Gluu. This method injects a Java agent into a running JVM process. The agent attempts to patch the lookup() method of all loaded org.apache.logging.log4j.core.lookup. JndiLookup instances to unconditionally return the string “Patched JndiLookup::lookup()”
Here is a tool that will help hot patch log4j2 :
https://github.com/corretto/hotpatch-for-apache-log4j2
Update #1: Gluu updated a repository with Patching the Log4j vulnerability in Gluu Server https://github.com/GluuFederation/
References: CISA Alert (AA21-356A) – Mitigating Log4Shell and Other Log4j-Related Vulnerabilities
Here are some Log4Shell security advisories from various IAM vendors
Gluu: Click here for more information.
Okta: Click here for more information.
ForgeRock: Click here for more information.
Oracle: Click here for more information.
Resources: Apache Log4j Vulnerability Guidance – https://www.cisa.gov/uscert/apache-log4j-vulnerability-guidance
Want support with patching Log4Shell for your applications?
Contact us right now by clicking here, Sennovate’s Security Experts will explain everything on call in detail.
You can also write a mail to us at [email protected] or call us on +1 (925) 918-6618.
About Sennovate
Sennovate delivers custom identity and access management solutions and SOC solutions to businesses around the world. With global partners and a library of 1000+ integrations, we implement world-class cybersecurity solutions that save your company time and money. We offer a seamless experience with integration across all cloud applications, and a single price for product, implementation, and support. Have questions? The consultation is always free. Email [email protected] or call us at: +1 (925) 918-6618




