What is Privileged Access?
It is a term used to designate special access for a standard user. Privileged access allows organizations to secure their infrastructure and applications, to run business efficiently and maintain the confidentiality of sensitive data and critical infrastructure.
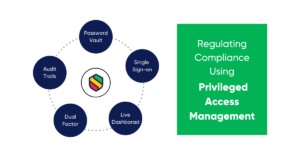
To manage and provide security to the user accounts having privileges to pre-eminent resources of the organizations, PAM solutions are implemented. Privileged Access Management is a procedure that uses technology to supervise, manage, and secure privileged accounts.
Here are some of the examples of “Privileged accounts”
- HR, Finance, and business privileged accounts.
- Local Administrator accounts
- Emergency accounts that have the right to shut down systems during the time of emergency
- The organization’s official social media handler
- Root user accounts and few others to list.
How are these accounts exposed to threats?
These privileged accounts are subjected to threats commonly due to the following reasons.
- Ex-employees’ accounts whose access to resources has not been restricted.
- Accounts that are seldom used and are abandoned.
So how can these privileges account
Generally, in organizations, some user have more access to company information than others such as the accounts of the Human Resource Administrator or the project manager, which catches the interest of hackers because these accounts have access to more critical areas of organizations. Many
data-breach incidents including famous ones like Starwood data-breach incident in 2016, “ADIDAS data-breach” in 2018, were the result of compromised management of ‘Privileged accounts’. According to one statistic, about
80% of
data breaches are due to theft of privileged credentials.
Is there any difference between PAM and IAM?
Both PAM and
IAM work on the same notion of providing security and ease of management of identities. However, IAM focuses on managing and providing security to accounts and identities of general users including customers, while PAM focuses on securing and managing user accounts having elevated access or privilege over the resources.
Having said this, PAM should always be given preference over IAM, as it is more crucial for any organization.
What are the considerable benefits?
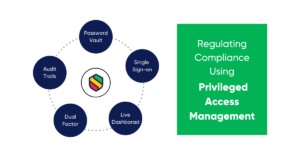
- Manage all Privileged users passwords using a secure vault
PAM allows you to manage passwords using one secure vault which is encrypted and safe enough to prevent cyber attacks.
- Manage and restrict your ex-employee’s access to the organization’s resources to prevent cyber threats by closing backdoors.
- Channelize accesses from a single spot (Single Sign-on)
Management of access to privileged accounts becomes hectic if each department of the organization handles this in its own way. Using PAM, this can be managed efficiently for the whole organization from a single point.
- Regulate restricted actions with the help of the session manager
PAM solution can give real-time updates if the account tries to perform restricted operations. Thus, administrators can abort those operations manually.
- Strengthen your IT compliance
Using PAM, organizations can supervise and audit all activities of “Privileged accounts” seamlessly.
PAM solutions have successfully reduced data-breach incidents associated with privileged accounts. Having said this, it is tremendously necessary for organizations to implement PAM solutions to secure their resources from threats and to ensure the best use of resources.
Sennovate is an industry leader in providing PAM and other identity access management solutions.
Learn more about our services by visiting our service page.