What exactly is OAuth 2.0?
OAuth 2.0 is a security standard, which lets one application to access data from another application without sharing your credentials.Let’s understand
OAuth 2.0 with a simple example, Imagine you’re playing an online game “race with me” and now you want to invite your friends via a social media account to play the game.In the initial days, you share your social media credentials to the game and “race with me” can get the contacts from your social media account, but the problem with that is “race with me” can access not just your contacts but your feed, messages and all other account details.So how do you stop that and share only the data that you want to share with the game, this is where
OAuth 2.0 comes into picture.
Understanding the OAuth 2.0 Terminology
- Resource Owner: User that give permission to an application to access another application’s data.
Example: you! you want to give “race with me” permission to access the “contacts” of your social media
- Client: Application that wants access to another application’s data on behalf of the Resource Owner
Example: “race with me”
- Authorization Server: Application which contains the data that the client wants to access.
Example: your social media account
- Resource Server: Application programming interface(API) that client wants to access. Most of the time Authorization Server and Resource are the same.
Example: API of your social media account to access your contacts.
- Scope: Data that Client wants to access or actions the Client wants to perform in the Authorization Server on behalf of the Resource Owner.
Example: “race with me” wants to access the contacts of your social media, so contacts will be added in the scope among other things that “race with me” wants from the Authorization Server.
- Redirect URI/Callback URL: Once Resource Owner gives permission to Client to access data from the Authorization Server, the Authorization redirects the Resource Owner back to the Redirect URI(back to the Client).
Example: once you give “race with me” permission to access the contacts in your social media account, you get redirected to the “race with me”. The URL that you get redirected to is the Redirect URI/Callback URL.
- Client ID: Authorization Server uses this ID to identify the Client
- Client Secret: A password only the Client and Authorization Server, the Authorization uses it to verify that the request came from Client.
- Response Type: The type of data Authorization Server sends back to the Client. Most of the time it is Authorization Code.
- Consent: Authorization Server verifies with Resource Owner whether it should let the Client access the data mentioned in Scope.
Example: Your social media asking you permission to let “race with me” access the contacts.
- Authorization Code: Once the Authorization Server gets Consent from the Resource Owner, it sends the Authorization Code to the Client.
- Access token: Authorization Server sends the Access Token to the Client and the Client sends Access Token to Resource Server in exchange for accessing the data or performing actions.
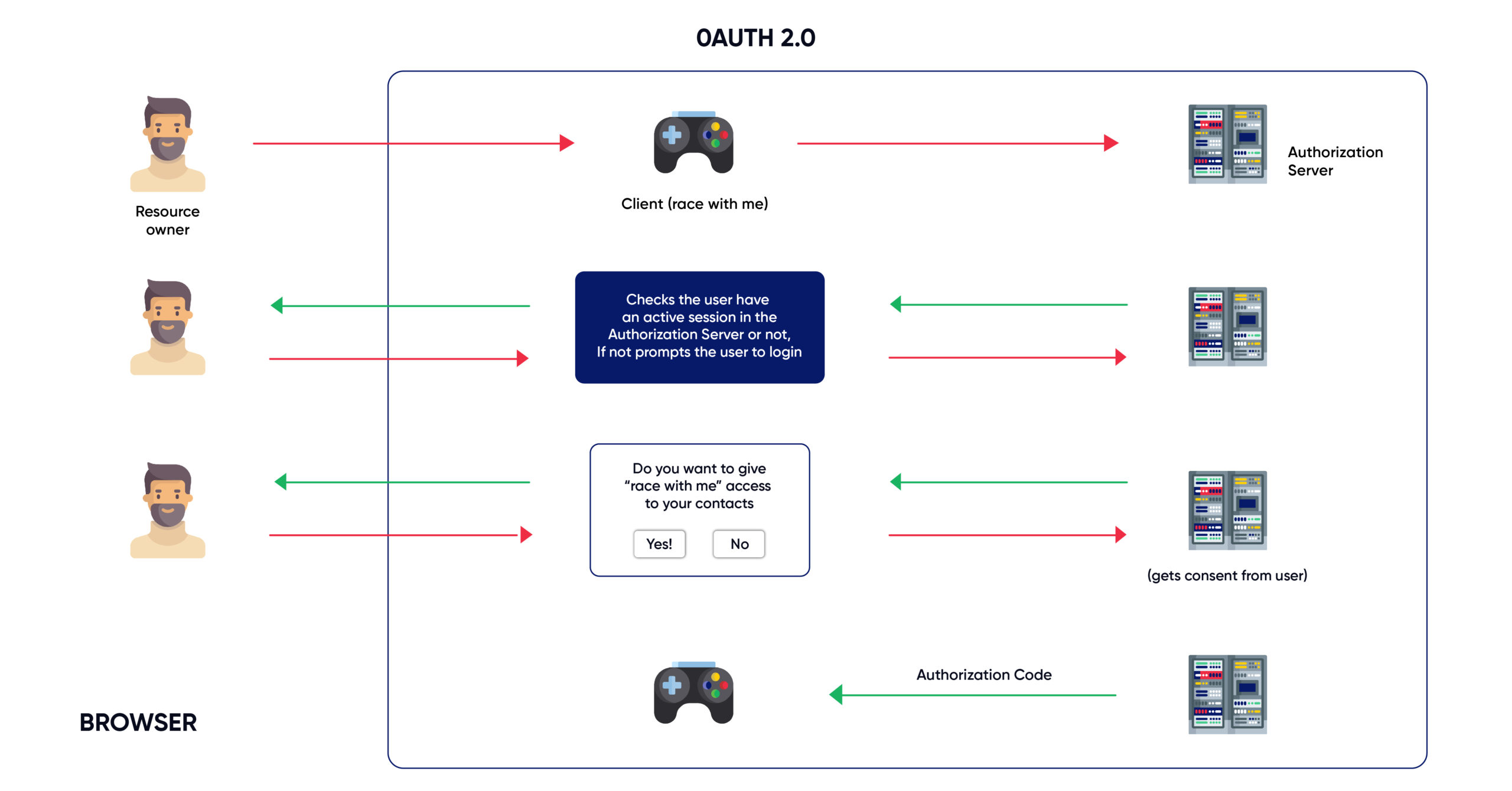
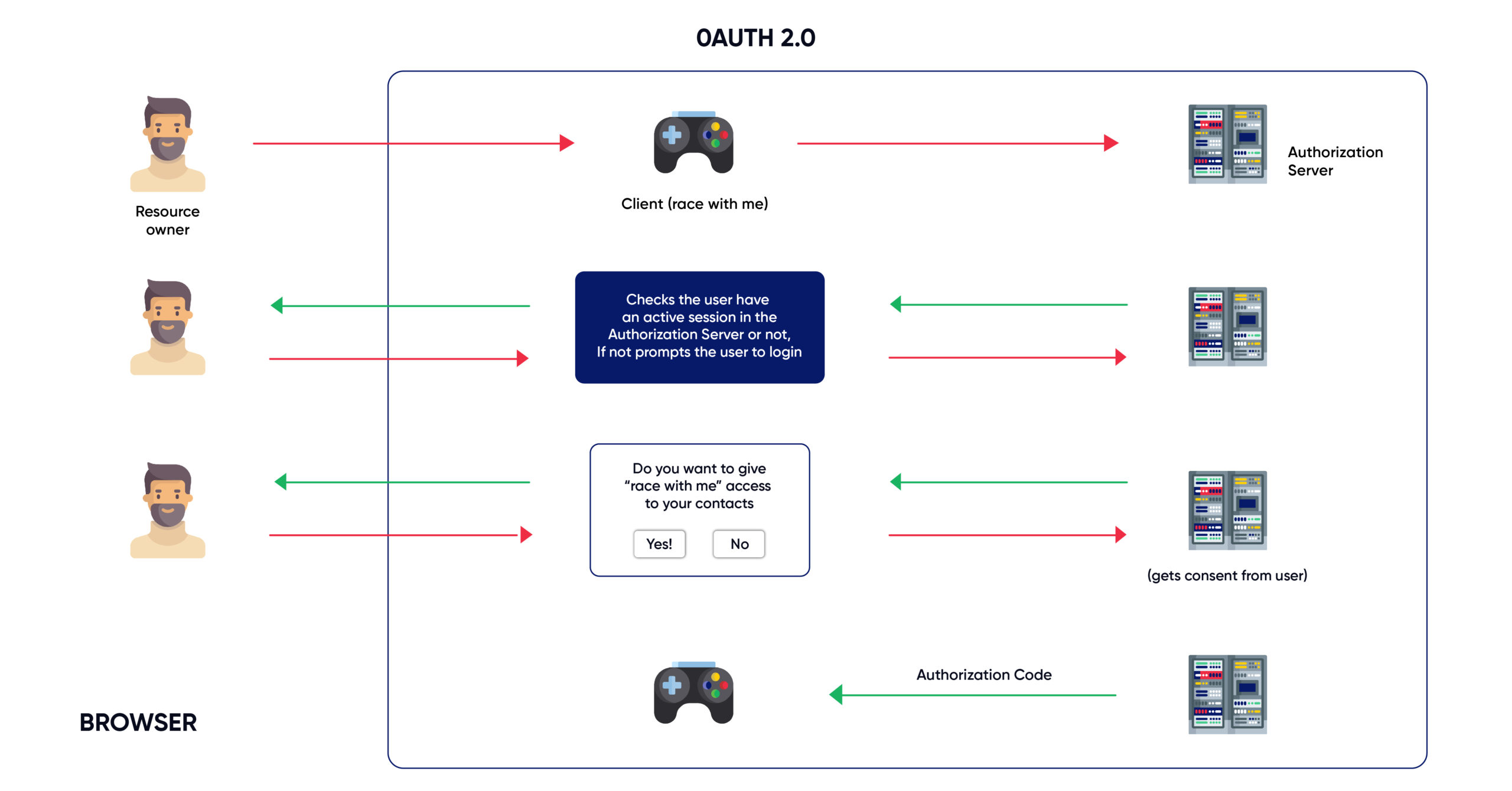
OAuth 2.0 Steps Happening via the Web Browser
- The Resource owner(you) wants to let the Client(Race with me) to access contacts in the Authorization Server(social media account).
- The Client redirects the browser to the Authorization Server with Client ID, Redirect URI, Response Type and Scope.
- The Authorization Server established a working relationship with the Client by sharing the Client ID and Client Secret for OAuth exchanges. This happened long before you granting permission to “race with me” to access the contacts.
- Scope will be the contacts.
- Response Type will Authorization Code.
- Redirect URI is where the Authorization Server will redirect the Resource owner, once the Resource owner gives permission to the Client to access the contacts.
- If the Resource owner already have an active session in the Authorization Server(already logged in), the Authorization Server asks for Consent from the Resource owner based on the Scopes requested by the Client. If the Resource owner isn’t logged in, the Authorization Server asks the Resource owner to login and asks for Consent.
- Once the Resource Owner gives Consent, the Authorization Server redirects back to the Redirect URI and sends Authorization Code to the Client.
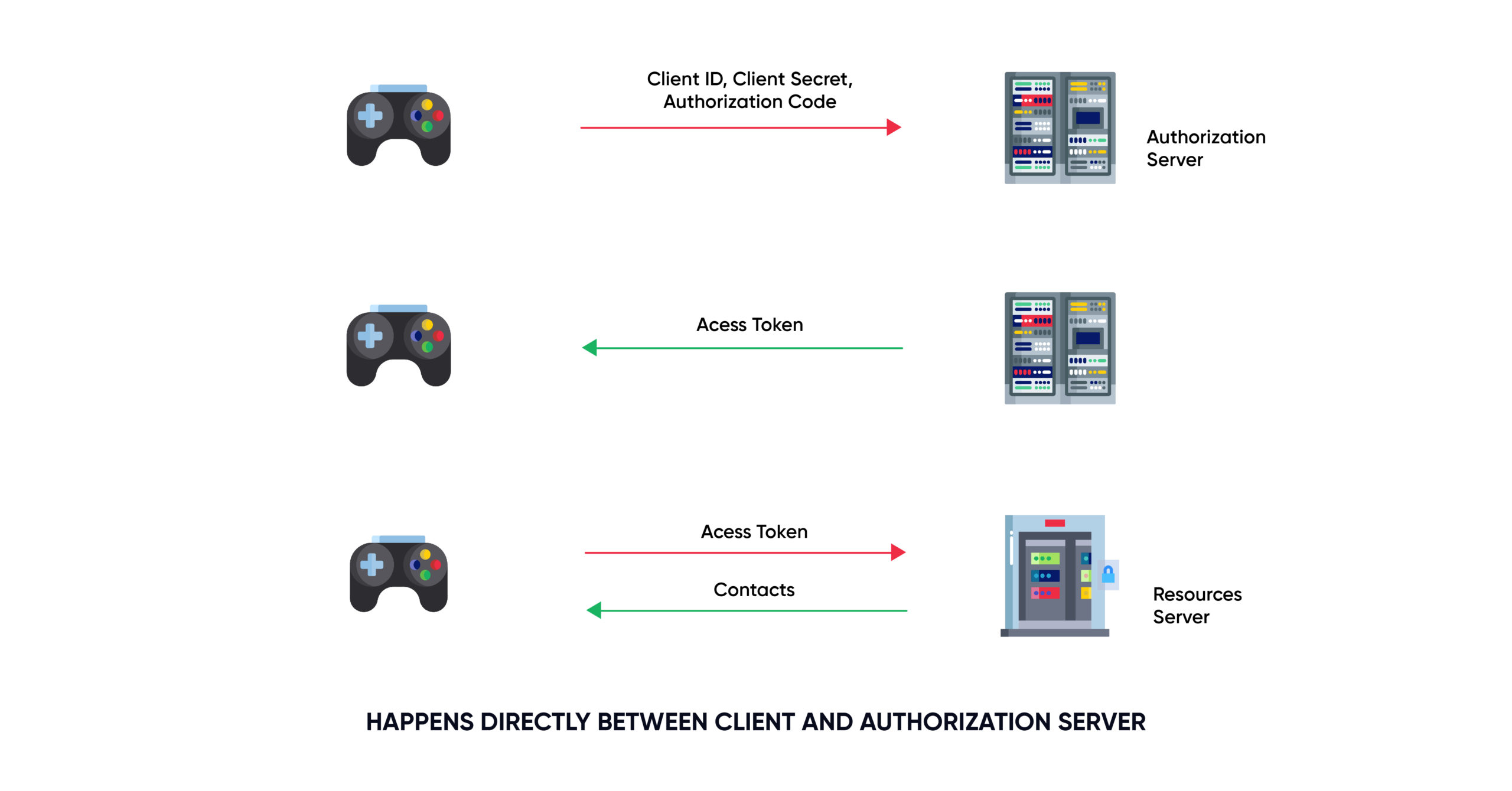
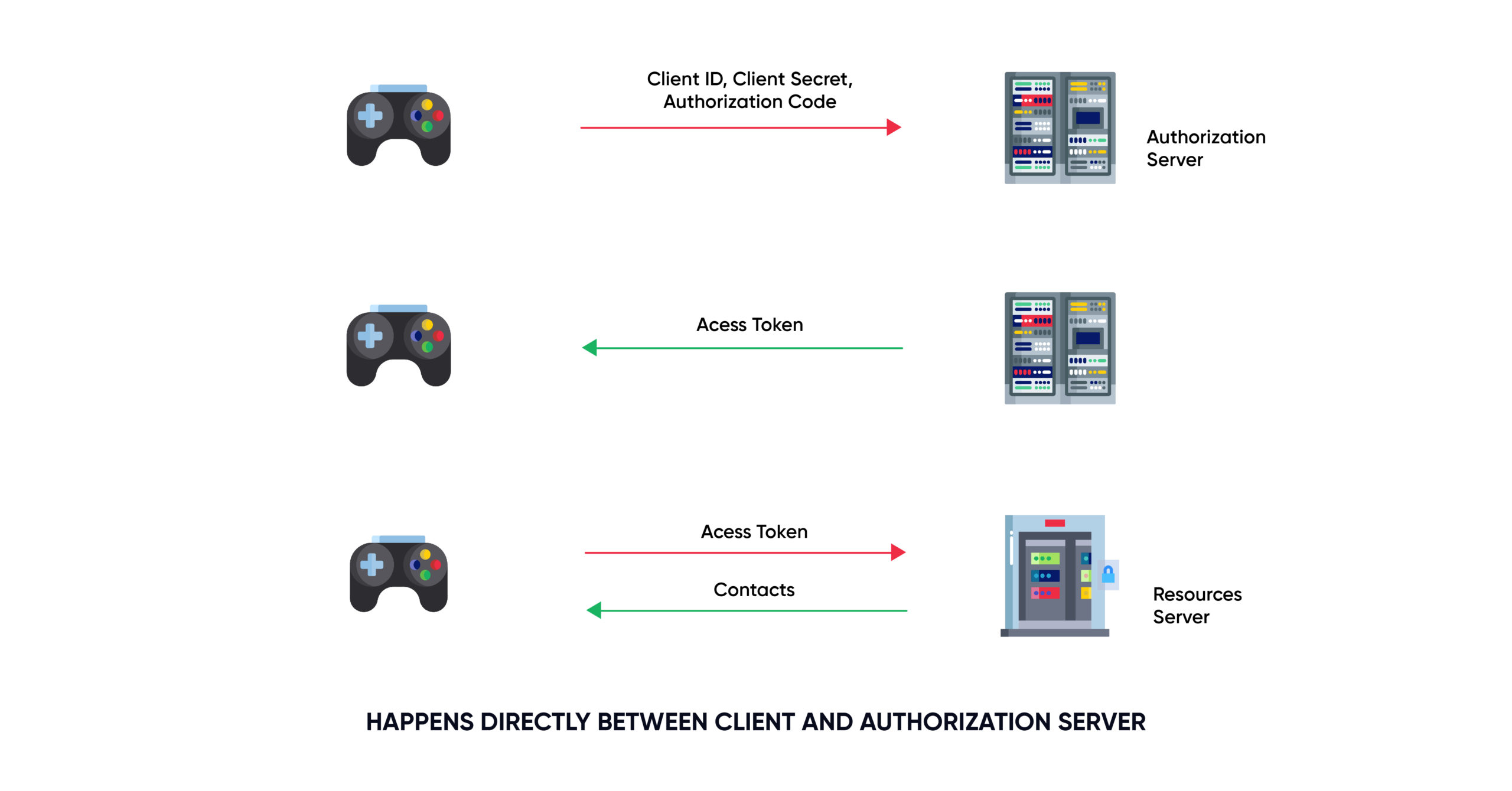
OAuth 2.0 Steps Happening directly between Client and Authorization Server.
- Once the Client gets the Authorization Code, it sends the Authorization code, Client ID, Client Secret to the Authorization Server.
- The Authorization Server verifies the Client ID, Client Secret, Authorization Code and send Access Token to the Client.
- The Client sends the Access Token to the Resource Server and gets access to your contacts.
Have questions about finding an
Identity and Access Management consultant?
Call +1 (925) 918-6618 the consultation is free.
About Sennovate
Sennovate delivers custom identity and access management solutions to businesses around the world. With global partners and a library of 1000+ integrations, we implement world-class cybersecurity solutions that save your company time and money. We offer a seamless experience with integration across all cloud applications, and a single price for product, implementation, and support. Have questions? The consultation is always free. Email
[email protected] or call us at: +1 (925) 918-6618.